Cloud

Office of the CTO Report: Continuous API Sprawl
APIs are a contract between the service provider and service consumer. When any application uses an API,...

Illumio CloudSecure: Cloud-Native Security Simplified
Gaining unified visibility into application traffic across multi-cloud, hybrid cloud and data center...
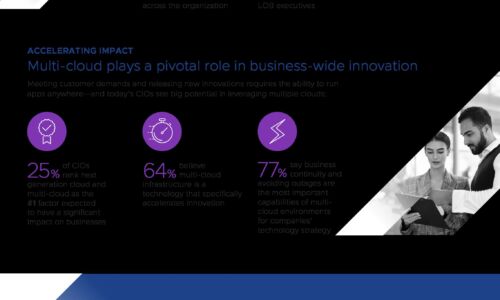
Forbes Study - CIO 2025
Important as the cloud already is, next-generation cloud and multicloud are expected to play even more...

How Cloudflare Bot Management Works
Cloudflare Bot Management applies automated, data-driven approaches to managing bots. By applying machine...

AI-powered contact centers to improve customer experience
Leverage AWS Language AI services to enhance customer experiences It's time to leave behind the challenges...

The Evolution of Cybersecurity
Cybersecurity Through the Years As we look at the ever-increasing, technology-dependent cyber environment...

CyberArk 2022 Identity Security Threat Landscape Report
A global report from CyberArk which shows that 79% of senior security professionals say that cybersecurity...

Securing web applications in healthcare
You might think that healthcare would not be a target for criminals, but WannaCry – a strain of ransomware...
2022 Cloud Threat Report, Volume 3
Cybercriminals are racing to exploit vulnerabilities, and the scope and damage potential of their cyber...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.