Authentication & Access Systems
The Top 5 Myths of Cloud Security
Hybrid cloud security is a hot topic, especially with the massive growth of public cloud providers like...

3 Ways to Reduce the Risk of Data Loss
Amid the fast-moving digital landscape, security risks are on the rise. People, devices, and objects...

Which WAF is right for me eBook
Despite the tech industry's collective best efforts to bolster secure application development practices,...
The Total Economic Impact™ Of The CB Predictive Security Cloud
Your endpoints are one of the most targeted assets in your organisation. In 2017 alone, more than 50%...

Protecting Data Capital in your Organization
The digital era is changing the way that organizations think about, protect, and monetize data. Now more...

20 Examples of Smart Cloud Security
Smart cloud security provides critical capabilities such as governing access and activities in sanctioned...

Securing Privileged Accounts: Three Steps to Maximize Protection with MFA
Hackers are eyeing your privileged accounts, so you better be using more than 'admin123' to secure them. Multi-factor...

10 Endpoint Security Problems Solved By The Cloud Infrographic
The three challenges you're likely facing – cost and complexity, defenses that can't keep up, and overburdened...
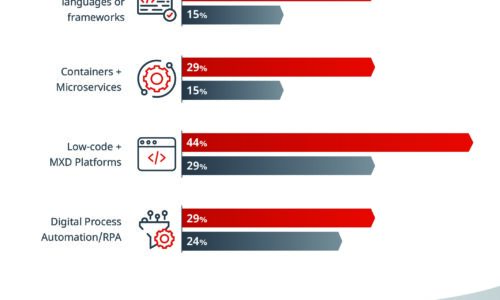
What Separates the Best from the Rest
Some IT organizations have the speed and adaptability to change course quickly when disaster strikes...

Cybersecurity Insiders: Cloud Security Report
The 2019 Cloud Security Report from Cybersecurity Insiders highlights what is and what is not working...

Optimized Security for Multi-Cloud laaS Environments
No question: Multi-cloud adoption can benefit your business. New question: How can you secure multi-cloud...
Accelerating Digital Transformation through Hyper-Converged Solutions
How can organizations simplify IT in order to improve business agility, enhance financial return on investment,...

Next-Gen Digital Transformation for Law Firms
Optimize opportunities to grow your practice and mitigate risk. Law firms, like other businesses, have...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.
