Artificial Intelligence
Employees are choosing how they work
'The measure of intelligence is the ability to change.' To remain connected, productive and secure in...

CDP Beyond Marketing
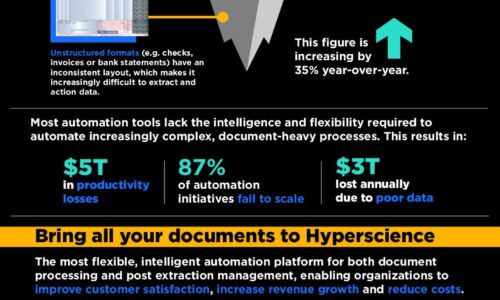
Speed. Quality. Low cost. There used to be a saying that you could only have any two at the same time....
10 Benefits of Oracle's Data Management Platform
Accelerating business change begins with the proper management of an organization's data. With Oracle's...
Economist: Signals and Noise: The New Normal in Cybersecurity
Cybersecurity is a top priority for Boards and the C-Suite. Strengthen your security posture with executive...
Report: Forward-Looking Technology for Retail CIOs
As the world continues to change, today's retail CIO is being asked to ensure technology can keep pace....
BlackBerry Cyber Suite
The challenge of securing and protecting data and endpoints is not a new requirement, but today it is...

IDC research: Evolution of the Service Experience
How can service organizations and discreet manufacturing unearth new revenue streams, and ensure post-sales...
Instant data for real-time business results
Machine learning is evolving faster than ever – AI and analytics can give you the capabilities to become...

Spear Phishing: Top Threats and Trends
Cybercriminals are constantly refining their tactics and making their attacks more complicated and difficult...
Accelerate Your Cloud Journey with an Intelligent Data Catalog
There's a generational shift happening in data management. On-premises databases and data warehouses...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.