Server

The Forrester Wave™: Enterprise Email Security, Q2 2021
In a 25-criterion evaluation of enterprise email security providers, Forrester identified the 15 most...

Strengthening Critical Infrastructure Security
Advances to critical infrastructure technology is opening the door to threat actors and cyber attacks...
Demystifying Zero Trust
Enter zero trust, a cybersecurity philosophy on how to think about security and how to do security. Zero...

NAIKON: Traces from a Military Cyber-Espionage Operation
NAIKON is a threat actor that has been active for more than a decade. The group focuses on high profile...
Making the Grade: End-to-End Security in Education
While students are preoccupied with completing online school assignments and streaming educational videos,...
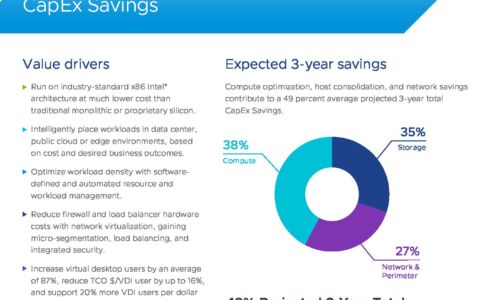
VMware Cloud Foundation: Maximise Digital Business Value
76% of IT organizations are committed to hybrid cloud as a long-term strategy to quickly adapt to changing...
Trusted Access Report
As global conflicts spill into the digital realm, protecting people through to the enterprise is increasingly...

The 10 Biggest and Boldest Insider Threats of 2019 and 2020
That risk is only increasing in an era of remote working and distributed teams. Without a holistic security...
Segmentation That Isn't Hard
Segmentation is a concept that has been around as long as we've been connecting networks. It is a proven...

97% of data sits unused by organisations
Data has the capability to transform your business, but only if it's collected and processed in the right...

Adaptive Cloud Security for AWS
Amazon Web Services (AWS) is the largest provider of cloud computing services worldwide. AWS pioneered...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.