SAN

CDP Beyond Marketing
Speed. Quality. Low cost. There used to be a saying that you could only have any two at the same time....
Managing the Cybersecurity Skills Shortage
The cybersecurity skills shortage has grown more urgent in recent months amid 'The Great Resignation'...

An introduction to ITM
As organisations move towards a more distributed workforce, the traditional perimeter of the office network...
Is Office 365 Giving your Network Heartburn? SD-WAN is the remedy
Speed, scalability, economics, and the promise of innovation are driving companies to the cloud. By 2021...
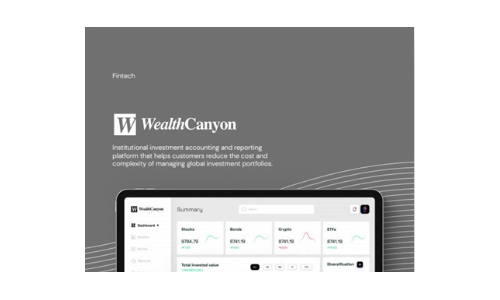
Wealth Canyon
Software companies in the financial industry, such as WealthCanyon, face challenges in collecting and...

Optimizing Workload Placement in Your Hybrid Cloud
Many IT organizations are in the process of modernizing their infrastructure, as part of either a digital...

NAIKON: Traces from a Military Cyber-Espionage Operation
NAIKON is a threat actor that has been active for more than a decade. The group focuses on high profile...

An Authentication Authority at Your Fingertips: PingFederate
Having an authentication authority within your infrastructure allows you to have a single source of truth...
NoSQL for Dummies
This easy to read guide to NoSQL databases provides the type of no–nonsense overview and analysis that...

Box and ECM: Key integrations that drive digital transformation
Box and ECM: Key integrations that drive digital transformation Legacy ECM solutions simply can't keep...
Beyond Awareness Training
Building a Sustainable Security Culture – and Why it Matters. Most cybersecurity leaders know that...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.