SAN

Hybrid Work: Why it's time to move your on-premises PBX to the cloud
For years, the shift to cloud-based communications services was gradual, with some organizations going...

Activate ESG Use Case Guide
Incorporating robust ESG practices into business strategy and execution is critical, not only to be a...

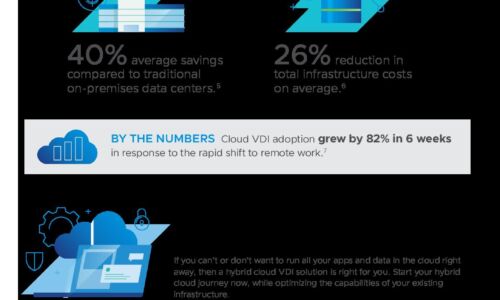
Supercharge your digital workspace
Delivering a great user experience is everything. You already know the advantages of secure digital workspaces...

Rethinking Insider Risk in the Gig Economy
More and more companies are relying on gig, contract and freelance workers to scale their business. Fully...

Slack is Custom-Built for Enterprise Companies
Over the past few weeks, we've all been challenged to rethink how our teams work together. We've had...
A Zombie's Survival Guide in a Changing Database World
With the rise of autonomous databases – and all the other scary changes in database management systems...
Report: An Executive's Guide to Industrial Cybersecurity
As enterprises invest heavily in digital transformation, industrial cybersecurity will increasingly serve...

Defending Ukraine: Early Lessons from the Cyber War
The latest findings in our ongoing threat intelligence efforts in the war between Russia and Ukraine,...
Top Workplace Trends 2023 (and Why Communications Are Essential)
What changes are coming for your organization in 2023? Looking ahead is essential for successful businesses....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.