SaaS

The SIEM Buyer's Guide for 2020
In 2020, security information event management (SIEM) solutions will be far more than an information...
Upgrading Quest Toad for Greater Security
IT administrators are right to draw a line in the sand when it comes to the software they install –...

Maintaining ‘Business As Usual' In Unusual Circumstances
The phrase 'business as usual' has a reassuring quality. It represents an ideal state in which the company...

WAAP Buying Guide
Organisations that strive to deliver secure digital experiences will achieve competitive advantage by...

Veritas Ransomware Resiliency Research for EMEA
Digital transformation, and especially cloud adoption, has accelerated due to the global pandemic. Needing...

WAN & Security Transformation whitepaper
Successful WAN and security transformation requires examining crucial questions: What's the role of a...
Does Your Data Integrity Need a Check-Up?
In the Healthcare and Pharmaceutical industries, data integrity can be a matter of life or death. Patients...

Protecting Every Edge To Make Hackers' Jobs Harder, Not Yours
Today's users need a network that allows them to connect to any resource from any location using any...
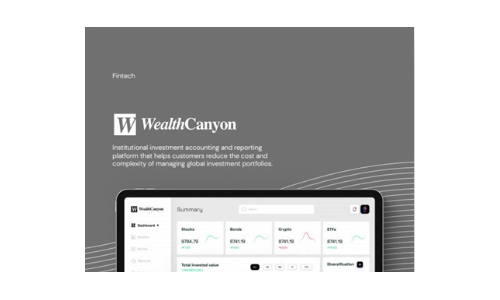
Wealth Canyon
Software companies in the financial industry, such as WealthCanyon, face challenges in collecting and...
Seven reasons why your enterprise needs intelligent search
Organizations are hungry to use data to grow and improve performance, but enterprises are struggling...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.