Operating System

Raising the Bar for Web Application and API Security Solutions
Securing the web applications and APIs that underpin cloud architectures is a challenge for security...

A Blueprint for Containers and Orchestration Best Practices
Containers enable agile deployment capabilities, requiring less coordination and oversight than on-premise...

Enterprise Backup and Recovery Made Easy
Protecting enterprise data in a complex IT environment is challenging, time-consuming, cumbersome and...

Build better endpoint security to protect your entire network
The threat of a serious cyberattack is nothing new — but the situation just keeps getting more complex....
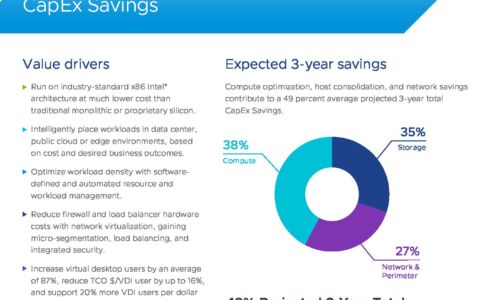
VMware Cloud Foundation: Maximise Digital Business Value
76% of IT organizations are committed to hybrid cloud as a long-term strategy to quickly adapt to changing...

EMA Report: Availability and Buying Options in the Emerging SASE Market
Cloudflare One reviewed as a leading provider of Secure Access Service Edge Gartner's Secure Access Service...
Web Coding and Development All-in-One For Dummies
Speak the languages that power the web. With more high-paying web development jobs opening every day,...
Trusted Access Report
As global conflicts spill into the digital realm, protecting people through to the enterprise is increasingly...
5 Things You Might Not Know About Cloud Security
Many organizations underestimate the security risks of the cloud, often assuming public cloud providers...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.