IT Security

7 Characteristics of Successful Hybrid Cloud Strategies
According to Gartner, by 2020, 75% of organizations will have deployed a multiload or hybrid cloud model....
A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...
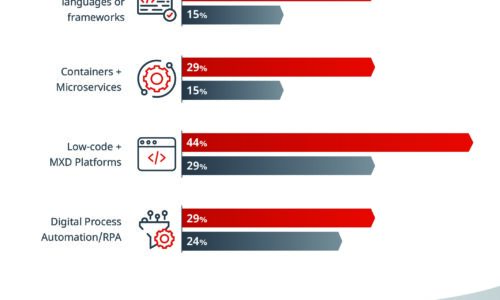
What Separates the Best from the Rest
Some IT organizations have the speed and adaptability to change course quickly when disaster strikes...
How to Tackle Ransomware by Managing Human Risk
CybSafe's analysis of ICO data finds the number of incidents of ransomware reported has doubled in a...
NoSQL for Dummies
This easy to read guide to NoSQL databases provides the type of no–nonsense overview and analysis that...

Ransomware Survival Guide
Be Ready for Ransomware Ransomware is an old threat that just won't go away. While overall volumes have...

What You Don't Know Can Hurt You: Expert advice on measuring risk
Managing risks begins with measuring risks. But how do you measure risks accurately? How do you share...
Next-Generation Anti-Malware Testing For Dummies
How did you choose your anti-malware solution? Did you put it through the same rigorous process as your...
SaaS Security Solution Checklist
SaaS applications have provided tremendous value to end users due to their easy setup and collaboration...

How to Stop Ransomware Attacks
This ebook How to Stop Ransomware Attacks provides in-depth guidance for quickly setting up stronger...

Managing Insider Threats in Financial Services
Financial services firms are victims of almost a quarter of all security breaches. And insiders contribute...

Is Your WAF Keeping Pace with Today’s Advanced Threats eBook
As the threat landscape evolves, so must our security controls and countermeasures. Recent research from...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

