ERP
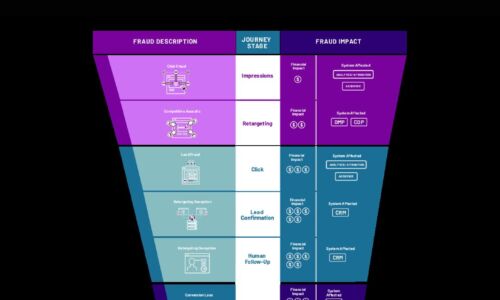
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

UCaaS: The Barriers of Buying
For many businesses, UCaaS (Unified Communications as a Service) is an attractive way to manage communications....
Next-Generation Anti-Malware Testing For Dummies
How did you choose your anti-malware solution? Did you put it through the same rigorous process as your...

Modern Data Analytics Guide: 7 Ways to Accelerate Business Insights
In the face of today's and tomorrow's challenges, does your organization have the data analytics tools...

Okta: Decoding Customer IAM (CIAM) vs. IAM
The world of Identity and Access Management (IAM) is rarely controversial. But today, there is a battle...
4 steps to enable a hybrid workplace
Every organization need to bring people and places safely together. It is an imperative to drive employee...
The Digital Business: What Do Your Customers Expect?
With every week that passes, our dependency on paper wanes as digital processes are introduced into every...
Endpoint security versus productivity in utilities: a false choice?
Utility companies are often targeted because they can be used so effectively as phishing lures, as they...

The benefits of on-prem cloud consumption models
As cloud computing becomes central to the IT service-delivery model, organizations are becoming more...

How Cloudflare Bot Management Works
Cloudflare Bot Management applies automated, data-driven approaches to managing bots. By applying machine...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.