Connectivity

The VMware Guide to Disaster Recovery Readiness
When it comes to data, planning for the unexpected is of paramount importance—especially today. But...
Introduction to AWS Security
Raise your security posture with AWS infrastructure and services. AWS's approach to security, including...
Artificial Intelligence: The Smarter Approach To Information Security
The news headlines are replete with stories of devastating data breaches, compromising the personal and...
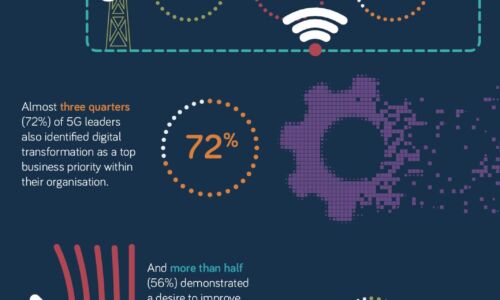
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...
Multi-tenant Datacenters and Sustainability
Colocation and wholesale services, collectively known as multi-tenant datacenters (MTDCs), form a key...

High Speed Network Encryption
High Speed Encryption (HSE) secures data in transit and data in motion, as it moves across the network...

Core connectivity as a key enabler for smart cities
With urbanisation continuing at breakneck speed around the world, governments need solutions to make...

Cloud-delivered security for the digital workspace
With the adoption of hybrid cloud and the rise in remote work, traditional connectivity models like VPN...

The Smart Factory
The manufacturing industry is experiencing major disruptions as traditional methods of producing goods...
Embrace Change: 4 Ways to Prepare for What's Next
Organizations large and small have been meeting the demand for hybrid work and learning environments,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



