Cloud Storage

The Multi-Cloud Maze: 5 Principles for Success
Organisations must now grow and pivot with previously unimagined agility. Enticed by the promises of...
Speed Up Your Digital Transformation With The Cloud
In this Content Services in the Cloud Guide by AIIM, we explore how companies are tackling critical document...

10 Hidden Costs of an On-Premises Phone System (PBX)
Many on-premise phone system (PBX) manufacturers claim that the five-year costs of their systems are...
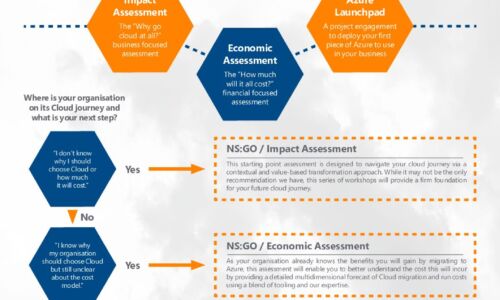
Azure Accelerator kit: Travel in the fast lane with New Signature
At New Signature, we understand that organisations are finding it difficult to start their Public Cloud...
Get to Know Cloud Content Management
By effectively managing your content with Cloud Content Management, you can reduce organizational friction,...

Securely Enabling a Hybrid Cloud in Microsoft Azure
The public cloud has rapidly moved past the novelty, curiosity stage to the business critical initiative...

Managing Multicloud: Getting the Fundamentals Right
Multicloud is a new concept for many organisations, yet it describes a trend that's been in place for...
Veeam 2019 Cloud Data Management Report
Over 1,500 business and IT leaders shared their approach to data management and its role in business...
Moving Endpoint Security to the Predictive Cloud
Traditional antivirus (AV) vendors aren't keeping up with today's threats. They don't protect against...

7 Experts on Moving to a Cloud-based Endpoint Security Platform
Without a doubt, endpoint security has become an urgent priority for many organizations, and it's not...

Manufacturing Transformation: Journey to the Cloud
Practical ways to achieve smarter, faster, and more responsive operations. Cloud is at the heart of digital...

A New Trend Explained: What is Multicloud?
Multicloud has become one of the buzzwords of modern IT, yet there's a lack of agreement on what it actually...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

