Cloud Storage

The Secure Cloud Advantage
Cloud computing has already transformed the way that businesses operate. As well as providing new efficiencies...
The 8 benefits of cloud and how you can achieve them for your business
Digital transformation is firmly upon us. In fact, Gartner predicts that 75% of businesses will transform...
The state of Office 365 backup
Barracuda commissioned independent market researcher Centropy to conduct a survey of IT decision makers...
Get to Know Cloud Content Management
By effectively managing your content with Cloud Content Management, you can reduce organizational friction,...

2018 State of the Enterprise Datacenter
With the Cloud and hyperconverged infrastructure continuing to be adopted by enterprise, it is only natural...

Securing Cloud Applications: Three Ways MFA Can Help
Many cloud applications authenticate users with passwords alone—an alarming notion considering the...
Cloud Platform Overview
A new age of cloud innovation is happening amid a backdrop of converging forces. Several technical and...

Moving Your Databases To The Cloud
Are you thinking about moving your Oracle databases to the cloud or making the transition to Database...

Enhance DevOps in AWS Cloud with NetApp
Read this technical white paper and discover new data management solutions that will improve development...

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...

Backup ROI for Dummies
Takeaways from downloading the executive brief: Why wait until something fails, breaks, is overwritten...
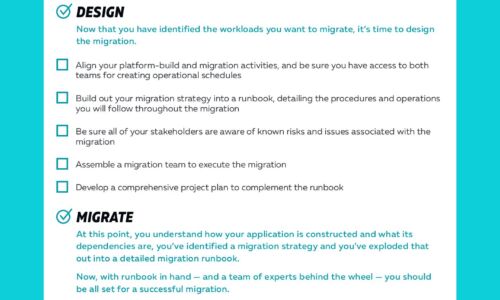
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...
Accelerate Your Cloud Journey with an Intelligent Data Catalog
There's a generational shift happening in data management. On-premises databases and data warehouses...
IoT Smart Cities & Buildings
Many of today's commercial buildings predate modern energy-saving tools and techniques. That means they...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.