Cloud Security

Multi-Factor Authentication Guide to On-Premise MFA
Despite the advantages of moving to the cloud and in spite of security assurances, there are still organisations...

2022 Threat Report
The BlackBerry 2022 Threat Report is not a simple retrospective of the cyberattacks of 2021. It is a...
Eight Critical IT Practice Areas That Drive Multi-Cloud Use Maturity
While most organizations are already using two or more clouds, most teams within the larger organization...

Zero Trust Network Access
VMware Secure Access provides enterprises a way for their employees to leverage a secure and fast connection...
Advanced Email Security
Email is a fundamental feature of modern business. Yet it is also the number one threat vector. Email...

8 Ways To Evaluate An MDR Provider
For many organizations, digital transformation had been a business initiative for years, but the pandemic...

Practical Guide To A Zero Trust Implementation
Zero Trust is becoming the security model of choice for enterprises and governments alike. However, security...
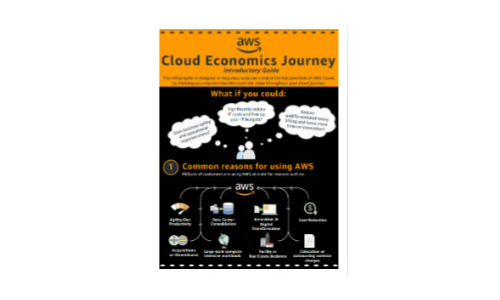
AWS Cloud Economics Introductory Guide
Discover the full potential of AWS Cloud and ways to maximise business value with this infographic. ...

Disaster Recovery in the Cloud with Cloud Volumes ONTAP
In this whitepaper, NetApp examines in detail the challenges involved in setting up a DR environment,...

2020 CIO Cloud Data Management Initiatives
According to the results of Frost and Sullivan's Digital Transformation survey, 99% of businesses are...
Edge Services Platform: Guide to vertical offerings
Aruba, a Hewlett Packard Enterprise company, is the global leader in secure, intelligent edge-to-cloud...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


