Backhaul

Connected cities and places
Improving digital infrastructure is key to enabling a smarter city or place to develop, thereby creating...
DDoS Threat Landscape Report: DDoS Trends from Q3 2022
DDoS attacks are growing larger, stronger, and more sophisticated. In Q3'22, we observed a resurgence...

EMA Report: Availability and Buying Options in the Emerging SASE Market
Cloudflare One reviewed as a leading provider of Secure Access Service Edge Gartner's Secure Access Service...
Implementing the NIST Zero Trust Architecture with Zscaler
The National Institute of Standards and Technology (NIST) has defined the core components of zero trust...

7 Ways to Work from Anywhere
Bring security and speed to the office of the future Following a massive global influx of remote work,...
Hybrid Work Drives the Need for ZTNA 2.0
The COVID-19 pandemic has had a profound effect on the world. Businesses have compressed into months...
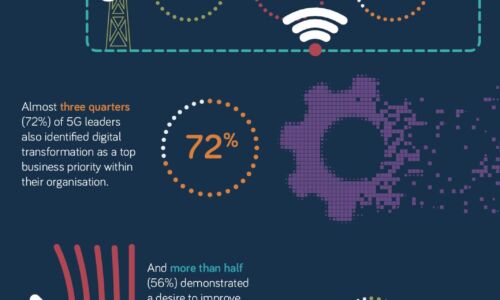
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

5G in the Transport sector
The Transport sector is pioneering the adoption of 5G connectivity, and yet it's doing so with quiet...

Core connectivity as a key enabler for smart cities
With urbanisation continuing at breakneck speed around the world, governments need solutions to make...

Getting Started with SASE
Secure Access Service Edge: A guide to secure and streamline your network infrastructure As enterprises...

The challenges and opportunities for smart cities
With urbanisation continuing at breakneck speed around the world, governments need solutions to make...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.