AIM

Zero-trust Solutions for Comprehensive Visibility and Control
Zero-trust solutions exist for nearly every part of the network. However, a piecemeal approach can leave...

CIO Roadmap to Hybrid and Multi-Cloud
While cloud has become a key driver of business expansion and operational efficiency, business and IT...

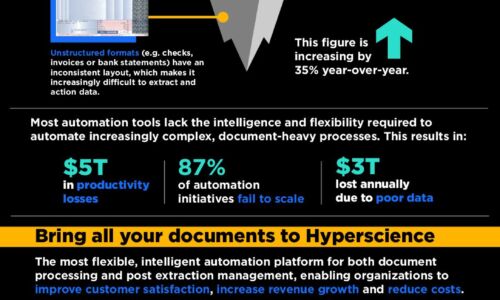
Winning in the New Era of Data Management
In the data-driven age, information is as valuable as currency. Entire industries are being disrupted...

Achieving transformative business results with machine learning
By providing the broadest and most complete set of machine learning (ML) services, AWS is able to meet...

Your Path to Cloud Analytics: 10 Key Considerations
Now more than ever, businesses are choosing SaaS for modern analytics. That's because today's vastly...
Challenging Times Call for a Cybersecurity Plan of Action
Could there be a more 'exciting' time to be a cybersecurity executive? Some might choose other adjectives:...

The Definitive Guide To SASE
What is Secure Access Service Edge (SASE) and why do you need it? Download the new guide to learn how...
Internal Firewalls for Dummies Guide
Organizations can no longer rely on edge firewalls alone to provide network security. Once attackers...

The Cybersecurity fail-safe: Converged Endpoint Management (XEM)
Organisations are experiencing more attacks than ever before. Cybersecurity Ventures expects a ransomware...

5-Step Buyers Guide to Multi-Cloud Management
Chart your roadmap to multi-cloud success by re-envisioning your approach to management on premises and...

ESG Zero Trust Impact Report
Cyberattacks have been rising steadily over the past two years as digital transformation has led to a...

What the Heck is IAST?
In this eBook, you will learn what IAST is and why it's much different than the previously well-known...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.